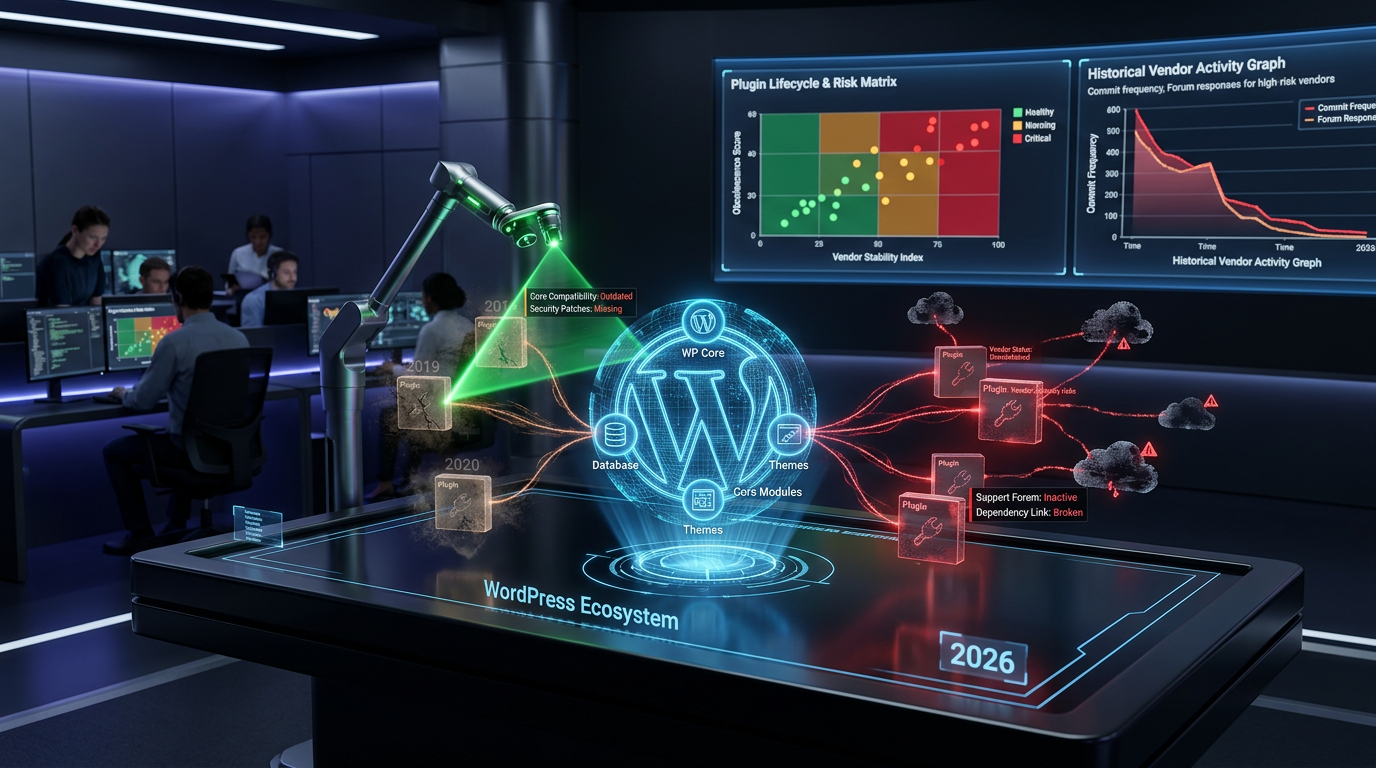
The Silent Archaeologists: Unearthing Latent Plugin Legacy & WordPress Database Schema Evolution in 2026
In the dynamic landscape of web development, understanding the architecture beneath your WordPress site is paramount. This article delves into the intricacies of the WordPress database schema, exploring how plugins leave their indelible mark and how this schema has evolved into 2026. As we embark on this archeological dig into latent plugin legacies, we’ll uncover critical insights for maintaining a secure, stable, and high-performance WordPress website.
For a deeper dive into mitigating such risks, consider exploring how The Silent Auditors: Unmasking Digital Forensics & Incident Response in WordPress Plugins (2026) can help.
Understanding the Core WordPress Database Schema Structure
The foundation of every WordPress installation is its database, a structured repository of all content, settings, and user data. The WordPress database schema is a predefined arrangement of tables, columns, and relationships that dictates how this information is stored and retrieved. Familiarity with this core structure is essential for debugging, optimizing, and extending WordPress functionalities.
At its heart, the WordPress database comprises several key tables, each serving a specific purpose. These tables are interconnected, allowing WordPress to efficiently manage various data types. Understanding these relationships is crucial for any developer or site administrator.
Key WordPress Core Tables
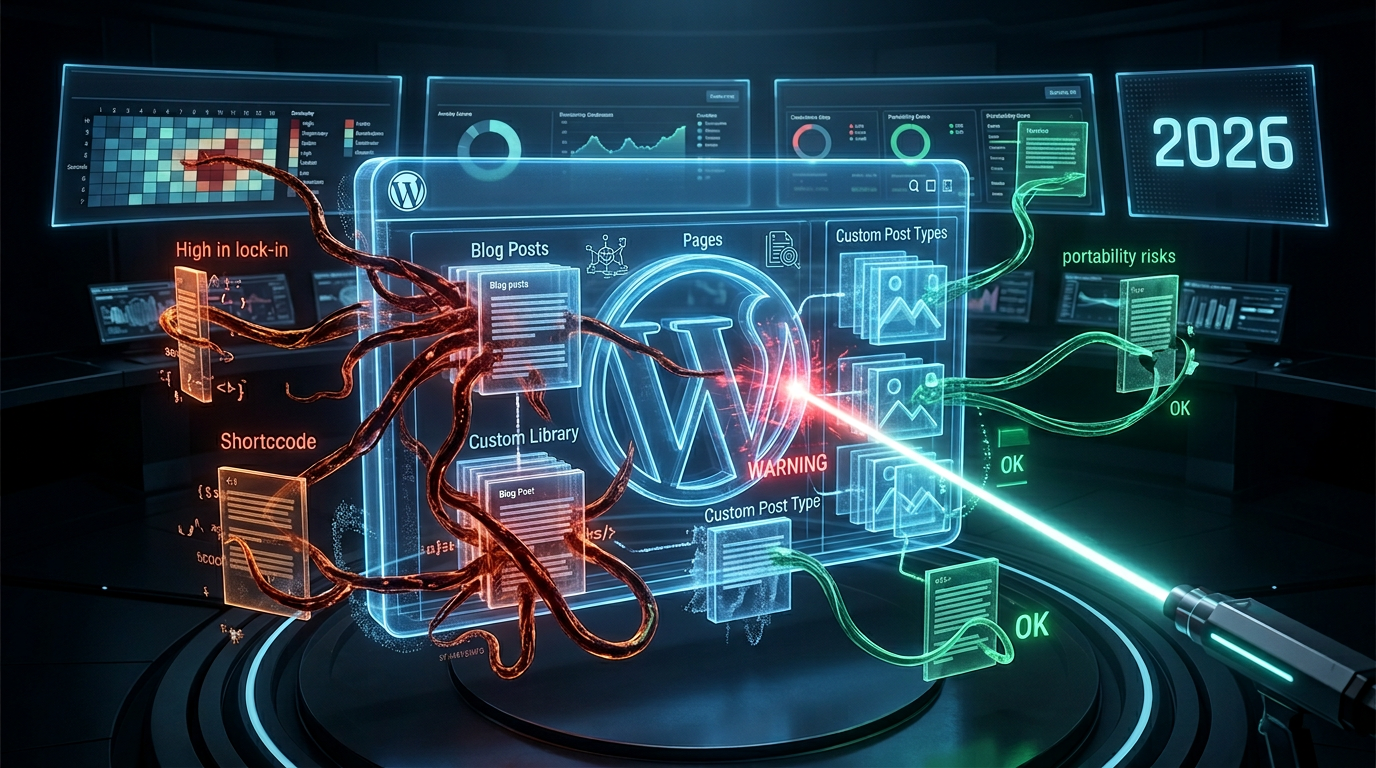
wp_posts: Stores all post types, including posts, pages, attachments, and custom post types.wp_users: Contains user information such as usernames, passwords (hashed), and email addresses.wp_comments: Manages all comments submitted on the website.wp_options: Houses various site settings, configurations, and transient data.wp_postmeta: Stores custom fields (meta data) associated with posts.wp_usermeta: Holds custom fields (meta data) related to users.wp_terms: Stores categories, tags, and custom taxonomies.wp_term_relationships: Links posts to their respective terms.wp_term_taxonomy: Describes taxonomies for terms (e.g., 'category' or 'post_tag').
Each table is designed with specific columns and data types, ensuring data integrity and efficient querying. The prefix wp_ is the default, but it can be changed during installation for security reasons, further customizing the WordPress database schema.
Evolution of the WordPress Database Schema
Over the years, the WordPress database schema has seen numerous refinements and additions to accommodate new features and performance enhancements. From the initial blogging platform to the robust content management system it is today, each major WordPress release often introduces subtle yet significant changes to how data is stored. For instance, the introduction of custom post types and taxonomies greatly expanded the schema's flexibility without compromising its core structure.
In 2026, the schema continues to be optimized for scalability and performance, addressing the growing demands of complex websites and diverse content strategies. Developers are constantly working to ensure that the database remains efficient and robust, able to handle massive amounts of data without performance degradation. This evolution also impacts how plugins approach digital twin and real-time simulation architectures.
Plugins as Architects: Reshaping the WordPress Database Schema
While the core WordPress database schema forms the backbone, plugins are the unsung architects that frequently extend and reshape it. Every plugin, from a simple contact form to a complex e-commerce solution, often introduces its own tables or adds custom fields to existing ones. This dynamic interaction is what gives WordPress its incredible versatility.
However, this flexibility comes with potential risks. The way a plugin modifies the database can significantly impact site performance, security, and long-term maintainability. Understanding these interactions is crucial for anyone managing a WordPress site.
How Plugins Modify the Database Schema
Plugins typically modify the database in a few key ways:
- Creating New Tables: Many complex plugins, such as those for e-commerce (e.g., WooCommerce), learning management systems (LMS), or membership sites, create their own dedicated tables to store their specific data. These tables often have intricate relationships with core WordPress tables and with each other.
- Adding Custom Fields (Meta Data): Plugins frequently utilize the
wp_postmeta,wp_usermeta, andwp_commentmetatables to store additional data related to posts, users, and comments, respectively. This is a common and flexible way to extend data without altering core tables directly. - Modifying Existing Options: Smaller plugins might store their settings within the
wp_optionstable, often serialized into a single entry. This can sometimes lead to an 'options bloat' if not managed carefully.
The extent and nature of these modifications depend entirely on the plugin's functionality. A well-coded plugin will manage its database changes efficiently, while poorly coded ones can leave behind a labyrinth of unused tables and options, known as "latent plugin legacy."
Risks Associated with Plugin Database Interactions
The power of plugins to alter the WordPress database schema also introduces several potential risks:
- Performance Degradation: Excessive or inefficient database queries introduced by plugins can slow down your website. This often stems from poorly designed custom tables or too many database calls on page load.
- Database Bloat: Uninstalled or poorly designed plugins can leave behind orphaned tables and options, significantly increasing the size of your database. This "database bloat" can impact backup times, migration processes, and overall query performance.
- Security Vulnerabilities: Insecure configurations or vulnerabilities in a plugin's database interactions can expose sensitive data. SQL injection, where malicious code is inserted into input fields to manipulate database queries, remains a significant threat if plugins don't properly sanitize and validate user input. This is also relevant in discussions around cross-compilation and binary injection risks in WordPress plugins.
- Compatibility Issues: Conflicting database modifications from multiple plugins can lead to unexpected errors or data corruption. This is particularly prevalent when plugins modify the same core tables or rely on incompatible schema versions.
- Data Integrity Problems: Bugs in a plugin's code can lead to incorrect data being stored, updated, or deleted, compromising the integrity of your website's content.
As of 2026, these risks remain at the forefront of WordPress site management, necessitating careful plugin selection and regular database maintenance. Understanding these risks is crucial, much like comprehending the implications of adversarial AI in WordPress plugins.
Unearthing Latent Plugin Legacy: Identifying and Mitigating Risks
The concept of "latent plugin legacy" refers to the residual database entries, tables, and files left behind by plugins that have been deactivated or uninstalled. This digital debris can accumulate over time, impacting performance, increasing security risks, and making database management more complex. Effectively managing this legacy is crucial for a healthy WordPress site.
Common Plugin-Related Threats to the WordPress Database Schema
Beyond general performance issues, specific threats impact the integrity and efficiency of the WordPress database schema:
- Outdated Code and Schema References: Plugins that haven't been updated in years might rely on deprecated database functions or make modifications based on older schema versions, leading to conflicts with current WordPress versions.
- Insecure Configurations: Poorly configured plugins might expose database administrator credentials or fail to encrypt sensitive data stored in custom tables. For solutions, see The Silent Cryptographers: Unmasking WordPress Plugins and Next-Gen Encryption in 2026.
- Excessive Permissions: Plugins requesting overly broad database permissions during installation can pose a security risk if compromised. A plugin should only have access to the data it explicitly needs to function.
- Third-Party Dependencies with Database Impact: Plugins often rely on external libraries or APIs that might introduce their own database tables or interact with the existing schema in unexpected ways. If these dependencies are not regularly updated, they can become a source of vulnerabilities.
- Lack of Proper Uninstallation Routines: Many plugins, upon deactivation or deletion, do not fully clean up their database footprint, leaving behind tables, options, and metadata. This contributes significantly to database bloat and latent legacy.
Identifying these threats requires vigilance and a proactive approach to plugin management and database analysis. Regularly reviewing your database structure can reveal hidden issues.
Strategies for Identifying Latent Plugin Legacy
To effectively unearth and address latent plugin legacy in your WordPress database schema, consider these strategies:
- Database Management Tools: Utilize tools like phpMyAdmin or specialized WordPress database optimization plugins to inspect tables. Look for tables with prefixes from uninstalled plugins.
wp_optionsTable Audit: This table is a common dumping ground for old plugin settings. Search for option names related to deactivated plugins. Be cautious when deleting, as some options might be shared.- File System Checks: While not directly database-related, remnants of old plugins in the
wp-content/pluginsdirectory can sometimes hint at associated database entries. - SQL Queries for Orphaned Data: Advanced users can run specific SQL queries to identify orphaned meta data (posts, users, comments) that no longer correspond to existing core entries.
Regular auditing is key to maintaining a clean and efficient database. In 2026, automated tools are increasingly available to assist with these tasks, making database health checks more accessible to non-developers.
Best Practices for Maintaining a Healthy WordPress Database Schema
Proactive maintenance is the cornerstone of a secure, stable, and high-performance WordPress website. Adhering to best practices for managing your WordPress database schema and plugin interactions is vital.
Secure Plugin Selection and Management
The first line of defense against database issues is Careful selection and management of plugins. Always:
- Choose Reputable Sources: Download plugins only from the official WordPress plugin directory or trusted commercial developers. For more insights on vetting plugins, consider consulting resources like the official WordPress Plugin Directory.
- Check Reviews and Update History: Prioritize plugins with high ratings, frequent updates (indicating active development and security patches), and good support. Look for plugins explicitly compatible with the latest WordPress versions in 2026.
- Assess Developer Practices: A reputable developer will often include proper uninstallation routines that clean up database entries when a plugin is removed.
- Limit Plugin Usage: While tempting to add numerous features, each plugin adds complexity. Only install plugins that are truly necessary for your site's functionality.
- Regular Updates: Keep all plugins, themes, and WordPress core updated to their latest versions. Updates often contain crucial security patches and performance improvements for the WordPress database schema.
Regular Database Optimization and Cleanup
Even with careful plugin selection, your database will accumulate data over time. Regular optimization and cleanup are essential:
- Database Backups: Before performing any optimization or cleanup, always create a full database backup. This is non-negotiable for disaster recovery.
- Optimize Tables: Use tools within your hosting control panel (like phpMyAdmin) or WordPress plugins to optimize database tables. This reorganizes disk space, reducing its size and improving access speeds.
- Delete Orphaned Data: Periodically delete old post revisions, unapproved comments, spam comments, and trashed items. Many free plugins offer this functionality.
- Identify and Remove Transient Options: The
wp_optionstable often stores transient data that should expire. While WordPress usually handles this, sometimes old transients remain and can be safely deleted. - Review Custom Tables: If you suspect a plugin has left behind tables, carefully review them. If you're certain they belong to an uninstalled plugin and contain no critical data, you can safely drop them. Exercise extreme caution here. For a general guide on database management, you might find articles from MySQL's official documentation helpful.
Implementing a routine schedule for these tasks will ensure your WordPress database schema remains lean and efficient.
Advanced Monitoring and Security Measures
For more advanced users and high-traffic sites, consider these additional measures:
- Database Monitoring Tools: Utilize specialized monitoring tools that alert you to slow queries, unusual database activity, or excessive resource consumption.
- Firewall Protection: Implement a robust web application firewall (WAF) to protect against SQL injection and other database-related attacks before they reach your server.
- Principle of Least Privilege: Ensure your WordPress database user only has the necessary permissions. Avoid giving full administrative rights if not absolutely required.
By taking a comprehensive approach to plugin management, regular optimization, and robust security, you can ensure the health and longevity of your WordPress database schema.
As we navigate the complexities of WordPress in 2026, understanding and actively managing the database schema remains a critical skill for all site administrators and developers. The silent archaeologists of the web, scrutinizing every table and every line of code, are the ones who truly safeguard the digital heritage of their online presence.
Frequently Asked Questions

Written by Aras Akıncılar
Uzun yıllara dayanan WordPress deneyimine sahip bir siber güvenlik uzmanı olarak, eklenti ekosisteminin derinlemesine analizine odaklanıyorum. Güvenlik açıkları, performans düşüşleri ve uyumluluk sorunları üzerine hazırladığım makalelerle, WordPress kullanıcılarının sitelerini daha güvenli ve verimli hale getirmelerine yardımcı olmayı hedefliyorum.